Archiv whitepaperů
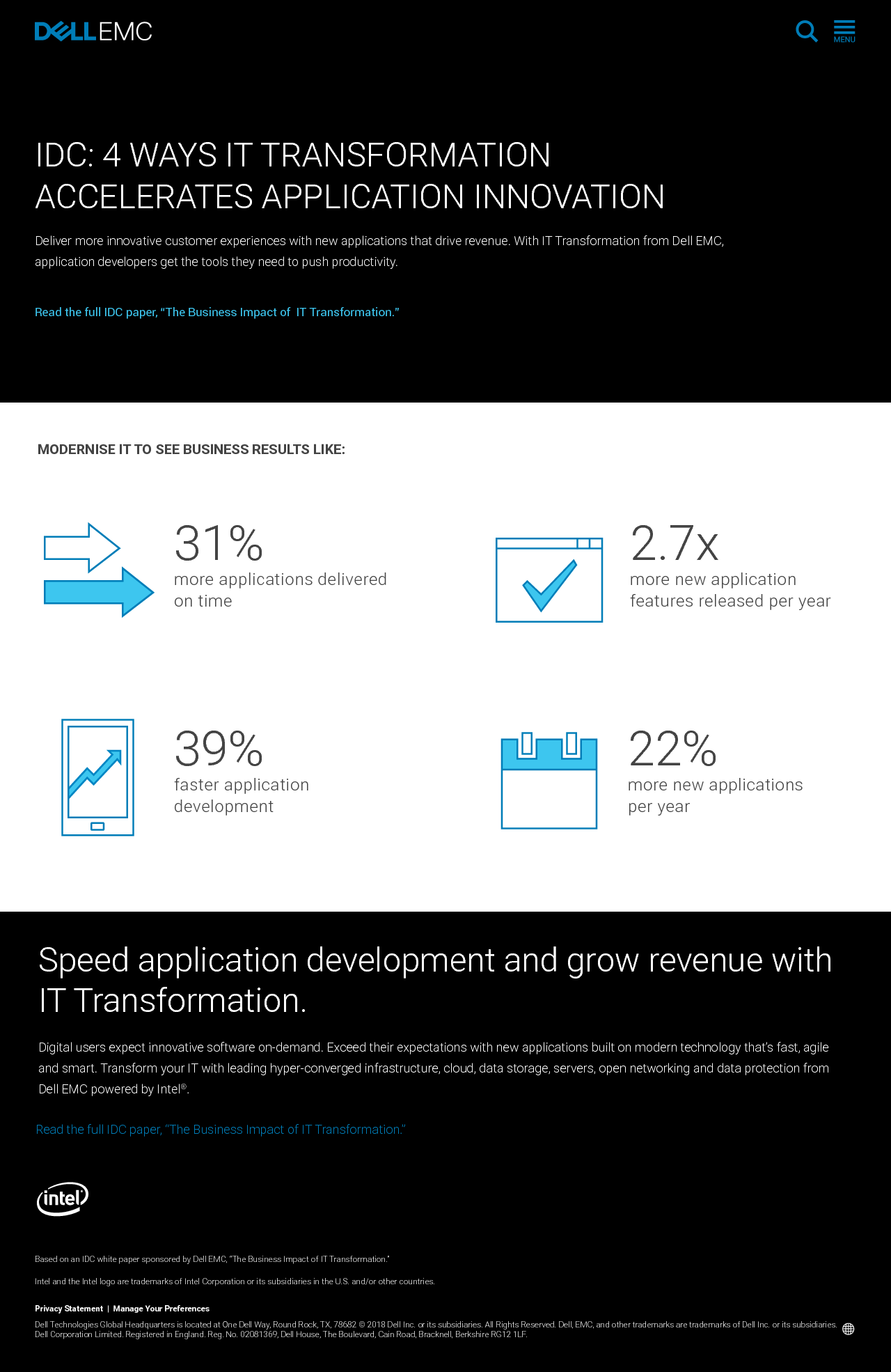
IDC: 4 Ways IT Transformation Accelerates Application Innovation
Deliver more innovative customer experiences with new applications that drive revenue. With IT Transformation from Dell EMC, application developers get the tools they need to push productivity. Dell EMC solutions powered by In...
IDC The Business Impact of IT Transformation Executive Summary
In today’s highly competitive, always-on business environment, IT must evolve from an enabler of back-office processes into an engine that helps multiply revenue. This evolution, called IT transformation (ITX), requires the wid...
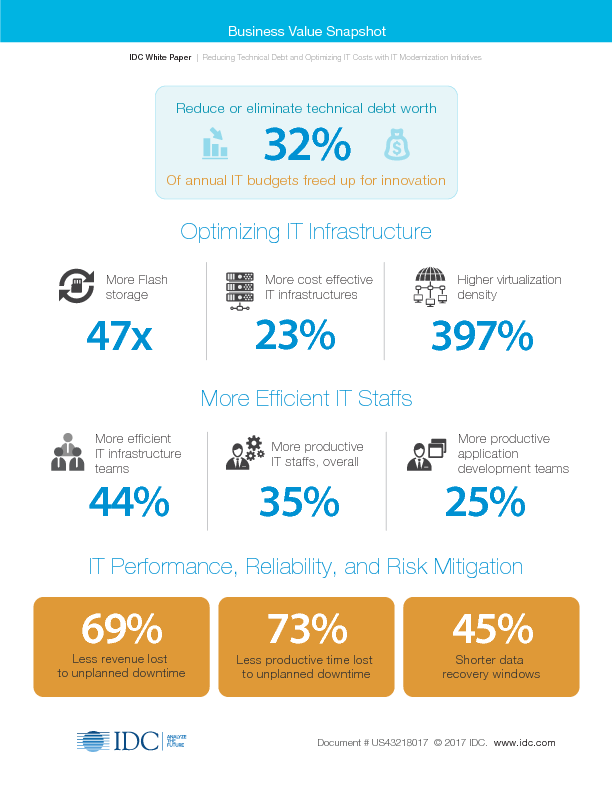
IDC The Technology Impact of IT Transformation Executive Summary Snapshot
Today, enterprise datacenters are under pressure; downtime because of system failure and human error is common and costly. To improve resiliency and support the level of agility needed to drive innovation, most enterprise datac...
IDC The Technology Impact of IT Transformation Executive Summary
Today, enterprise datacenters are under pressure; downtime because of system failure and human error is common and costly. To improve resiliency and support the level of agility needed to drive innovation, most enterprise datac...
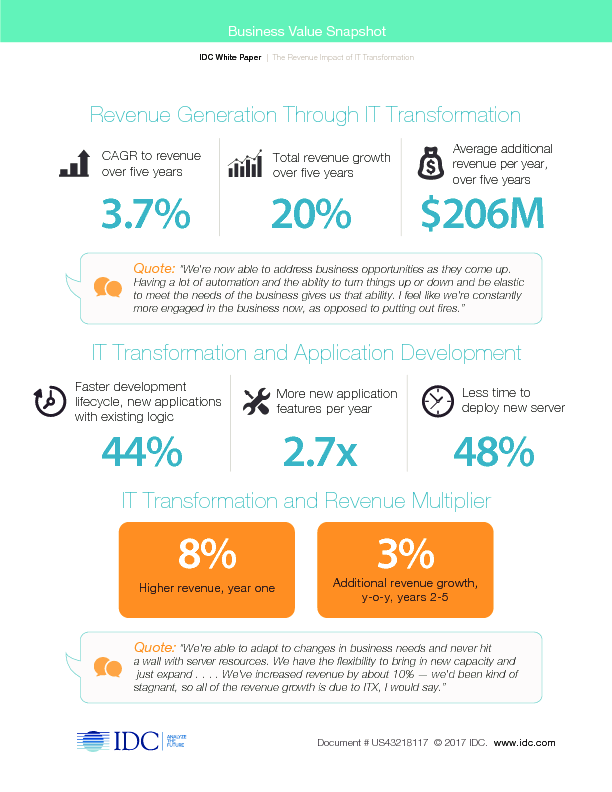
IDC The Business Impact of IT Transformation Executive Summary Snapshot
In today’s highly competitive, always-on business environment, IT must evolve from an enabler of back-office processes into an engine that helps multiply revenue. This evolution, called IT transformation (ITX), requires the wid...
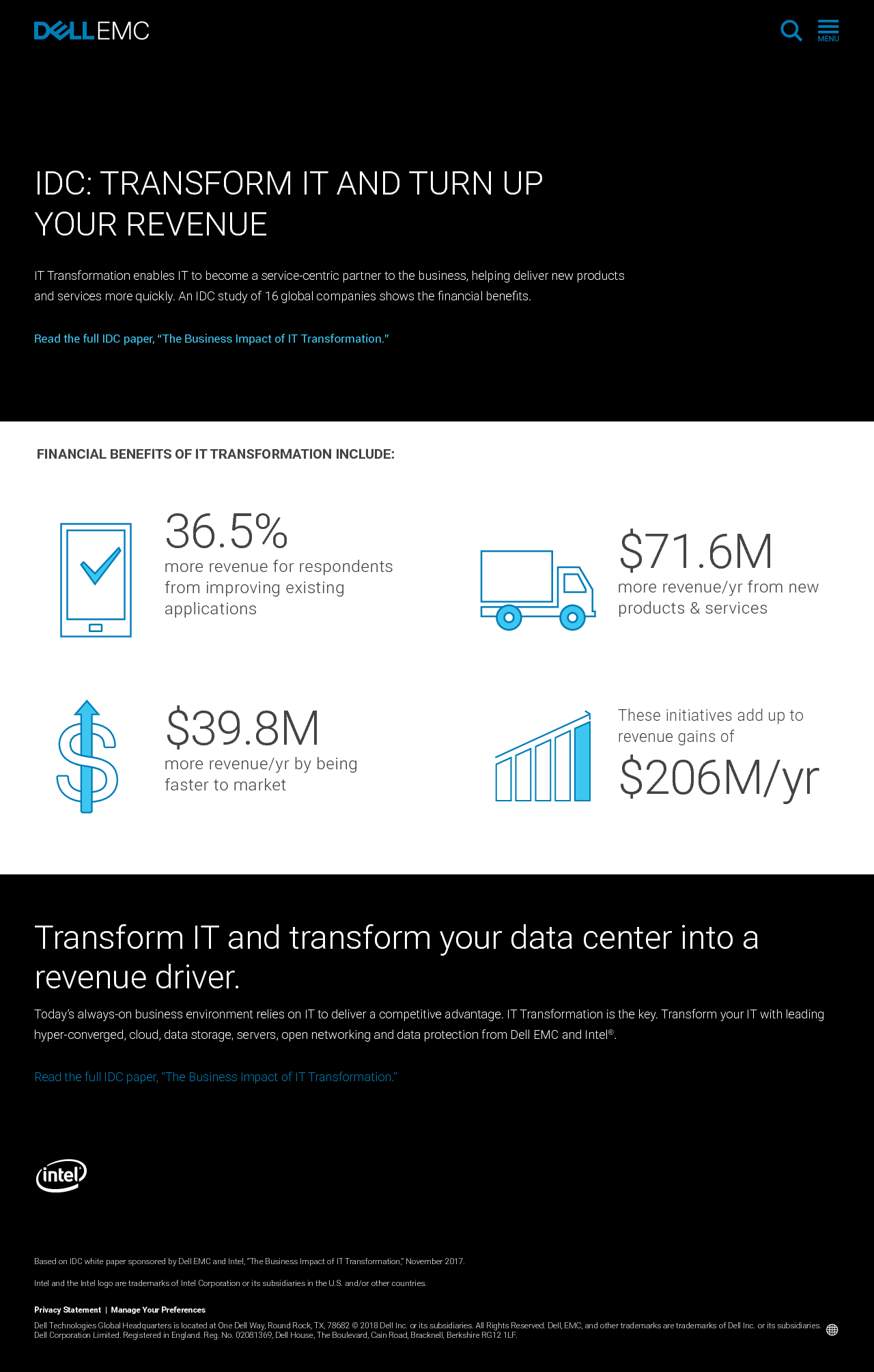
IDC: Transform IT and Turn Up Your Revenue
IT Transformation enables IT to become a service-centric partner to the business, helping deliver new products and services more quickly. An IDC study of 16 global companies shows the financial benefits. Dell EMC solutions powe...
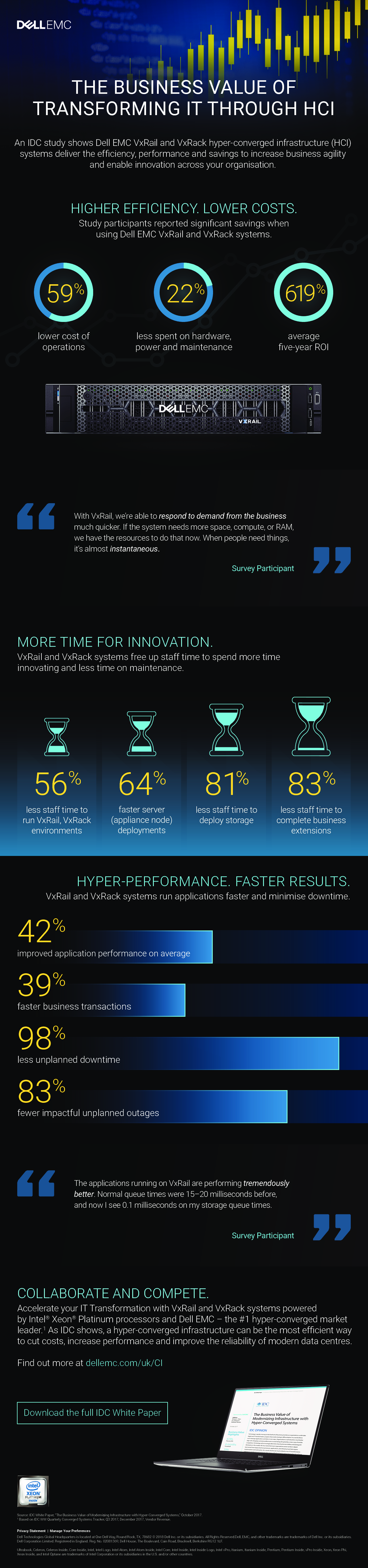
The Business Value Of Transforming IT Through HCI - Infographic
An IDC study shows Dell EMC VxRail and VxRack hyper-converged infrastructure (HCI) systems deliver the efficiency, performance and savings to increase business agility and enable innovation across your organisation. Dell EMC so...
Introducing the all-new Dell™ Precision™ mobile workstations
Experience unrestrained innovation with the thinner, lighter and premium-designed Dell Precision mobile workstations. Built with the latest 8th Gen Intel® Core™ i7+ vPro™ processor and Intel® Xeon® processor, blazing-fast memor...
Dell EMC PowerEdge R7415 AMD EPYC VMware vSAN Mixed Workloads Performance
Dell EMC provides VMware vSAN Ready Nodes that combine a wide range of Dell hardware and VMware vSAN software into a ready-to order package. These include the new single-socket Dell EMC PowerEdge R7415 servers powered by the AM...
4 Essentials For Turning The IoT Into Actionable Intelligence
Edge computing will soon become the new norm as we enter the era of zettabytes and billions of connected devices. Dell EMC PowerEdge servers are uniquely designed to meet the demands of edge computing with integrated security, ...