Whitepaper archive
Three Ways to Future-Proof Your Business
When times are uncertain, improve visibility and spend control to give your organization the certainty it needs. While having control over costs, cash flow, and compliance is important for businesses during typical times, it’s...
The Hidden Potential of VAT Reclaim
Levied by more than 160 countries, Value Added Tax (VAT) is one of the most common forms of taxation in the world. VAT is applied at every step of the manufacturing and supply chain – and collected by businesses on behalf of th...
Moving forward - How Better Spend Management Can Drive Better Decisions
To understand how businesses are turning today’s turbulence into business strength that will see them through to tomorrow’s opportunities, we commissioned EIU to survey 552 executives in 11 countries. The results show that mos...
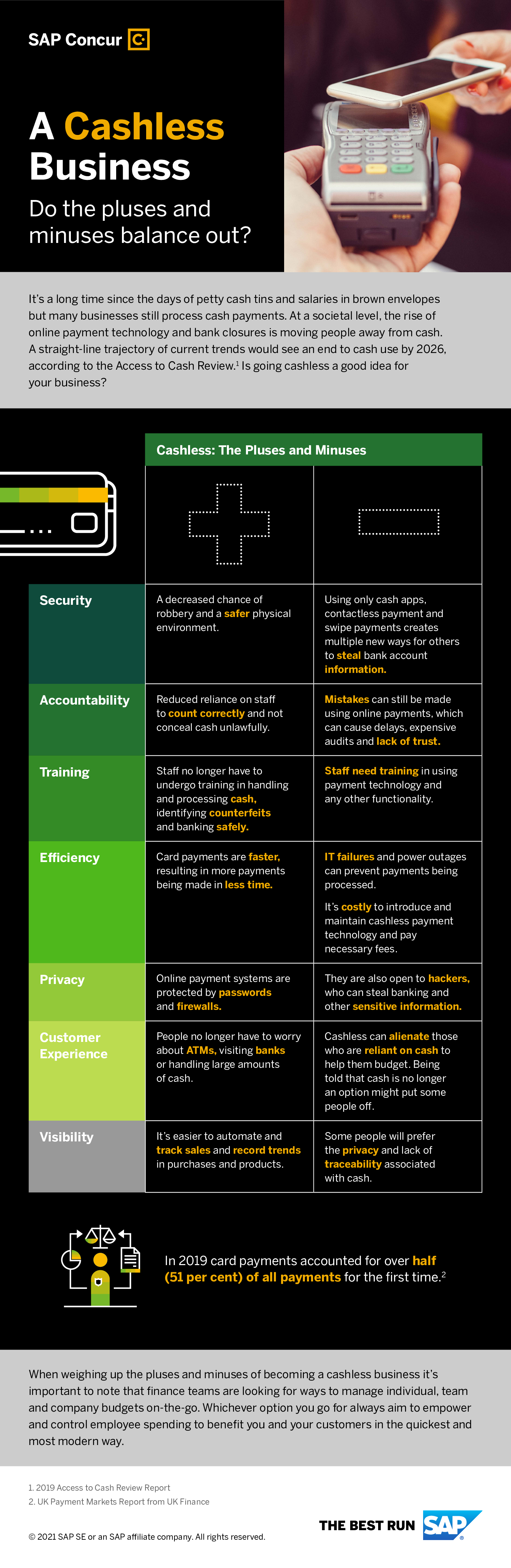
A Cashless Business - Do the pluses and minuses balance out?
It’s a long time since the days of petty cash tins and salaries in brown envelopes but many businesses still process cash payments. At a societal level, the rise of online payment technology and bank closures is moving people a...
Take Photos of Receipts to Gain Quicker Visibility of Spend
ExpenseIt: Create, Itemize, and Categorize Expenses Effortlessly: The toughest task on any trip is coming home to a pile of receipts. Help your employees eliminate this tedious task with ExpenseIt in the SAP Concur mobile app....
Your school’s Remote Learning journey starts here
Building a safe, reliable and user-friendly remote learning capability can be transformational and rewarding for students, teachers and parents alike. But for the staff tasked with choosing a remote learning solution, selecting...
Limitless learning - How schools are transforming education for the digital era
For Dell Technologies, limitless learning means uninterrupted access to the technology and applications required to deliver the best outcomes for students and schools. It also refers to the limitless access to information, oppo...
Transforming the way SCHOOLS consume technology
Your school’s technology has never been so easy to pay for, manage, and support. The way we consume products and services is changing fast, with a huge shift away from owning things to paying a fixed monthly cost for using wha...
FUTURE OF WORK - Embracing New Dynamics, Creating New Experiences
74% of IT and business decision makers surveyed globally consider employee experience (EX) a top business priority. Rise of this younger generation workforce is placing demands on workspace designs and policies. Almost 1/3 of ...
Onboard and Off-board Charging
Strong demand for electric vehicles is driving the growth of onboard chargers and electric vehicle charging stations. Battery electric, plug-in hybrid, and possibly fuel cell electric vehicles will require high power, cost-effe...