Архив проектных документов
The Total Economic Impact™ Of Slack For Technical Teams
Slack is a productivity and collaboration application utilized on a daily basis by technical teams, including developers, engineers, and IT staff. By consolidating their tasks within Slack using integrations and native workflow...
The future of intelligent productivity, powered by Slack AI
Knowledge silos kill companies. There’s data to prove it. In ‘The Crisis of Fractured Organisations’, global research firm Forrester found that the average worker spends 2.4 hours each day looking for the information that they...
How 9 businesses boosted productivity, efficiency and financial success with Slack and Salesforce
As economic uncertainty continues to dominate headlines, businesses are searching for ways to do more with less. Productivity, efficiency and cost savings are not just buzzwords, they’re necessities. If companies want to achiev...
Transform your customer service with real-time, white-glove support
Unlock the secrets of exceptional service with our White Glove Service Guide. Dive into proven strategies that redefine customer experiences. Explore key insights and practical tips to implement white glove service effectively....
The State of Work 2023: customer support trends
Discover the latest customer support trends that shaped the landscape in 2023. Our resource provides valuable insights into the state of work, offering a deep dive into customer support dynamics. Gain a comprehensive understand...
The Slack handbook for exceptional customer service
Delve into the world of exceptional customer service with our insightful handbook. Uncover proven strategies that set the standard for excellence. Explore key insights and practical tips to enhance your customer service approac...
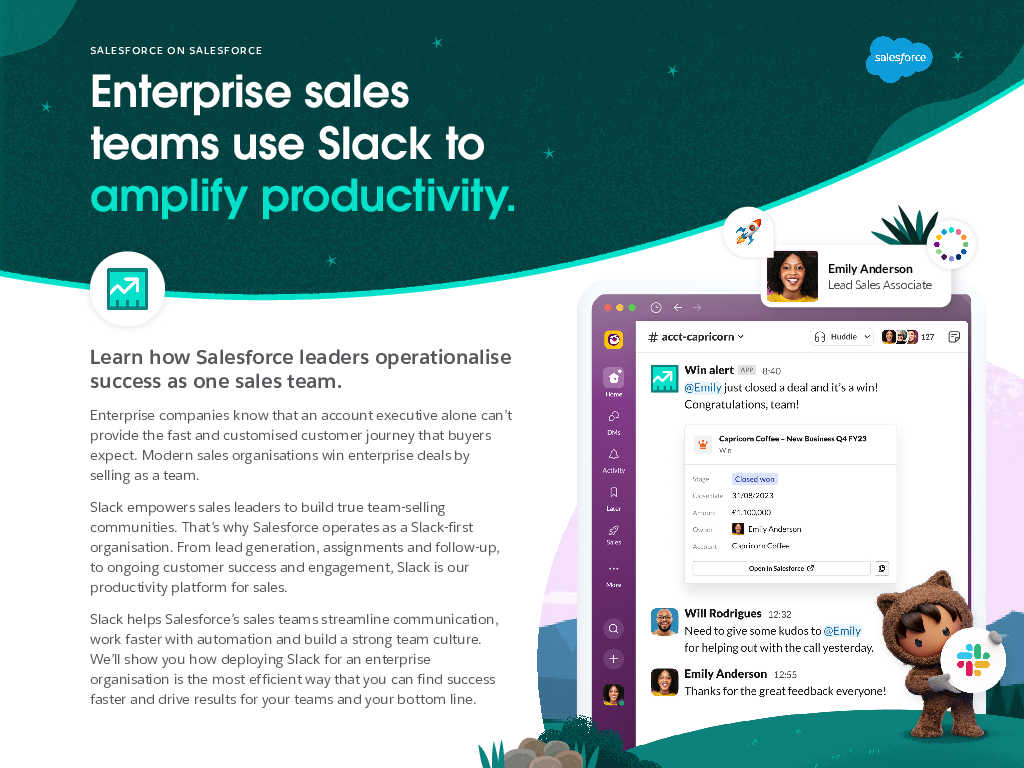
Enterprise sales teams use Slack to amplify productivity.
Explore the transformative power of integrating Salesforce with Slack in our latest whitepaper. Discover how enterprise sales teams amplify productivity through seamless collaboration. Gain valuable insights to optimize your sa...
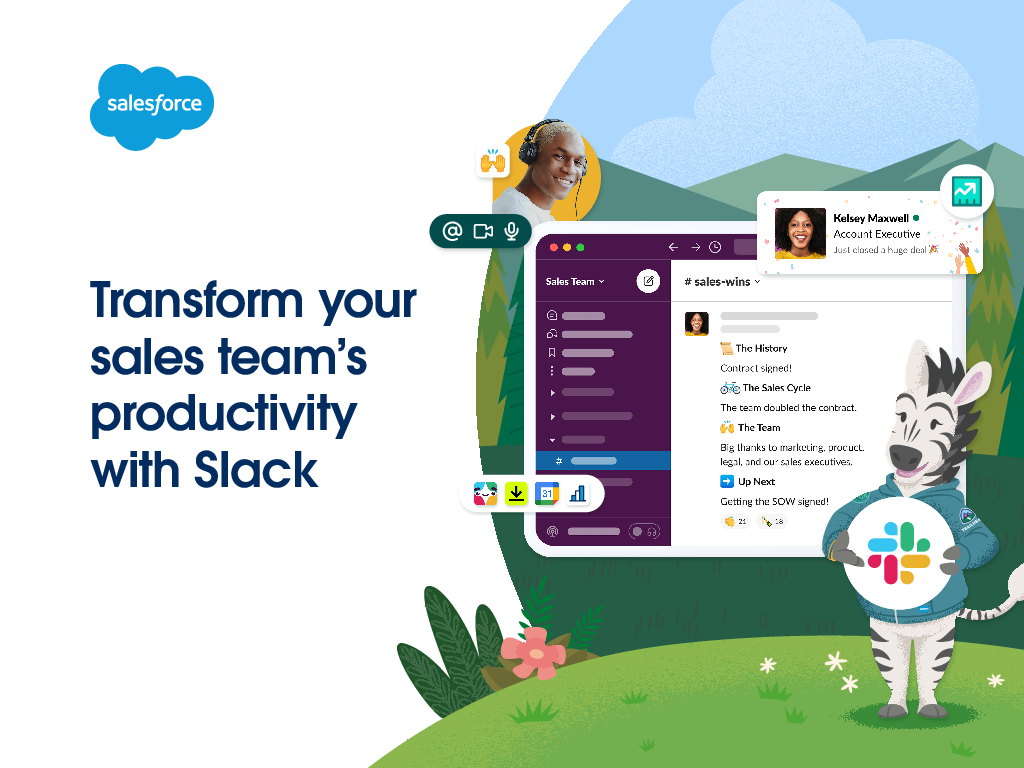
Transform your sales team’s productivity with Slack
Unlock the secrets to supercharging your sales team's efficiency with our latest whitepaper. Discover how integrating Salesforce with Slack can transform collaboration, streamline communication, and drive unparalleled productiv...
3 actionable ways you can add context to documentation
The “why” behind what your team is doing is just as important as the “how.” The “how” is operational, and often lives in documentation. Ask anyone at your company how to submit PTO, and they’ll all probably point you to the s...
Building a Cyber- Resilient Data Recovery Strategy
Building a holistic cybersecurity program can be complex and multifaceted. With threats mounting, cyberattacks, including ransomware, are an ever‑present danger. Organizations who leverage voluntary frameworks, such as the NIST...