Arsip buku putih
A New Role In Managing Uncertainty
The CFO role continues to grow and evolve as their analytical skills and insights become even more valuable in a climate of economic turmoil. SAP Concur Research found that 90% of senior finance leaders agree their key task tod...
Neural Manufacturing™
The manufacturing industry has witnessed different phases of change over the decades. Presently, transformation in operating models and emerging shifts in business models are forcing manufacturers to become future-ready. With N...
Alstom bets on data for future growth
As Alstom grew and evolved in the digital economy, it faced various challenges with managing its IT landscape, especially master and reference data, which was spread across multiple applications. The multinational rolling stock...
TCS Digital Transformation for SAP on Microsoft Azure
Accelerating digital transformation with SAP on cloud Businesses today are battling challenges on multiple fronts. They are for looking for suitable digital transformation solutions to overcome challenges related to business g...
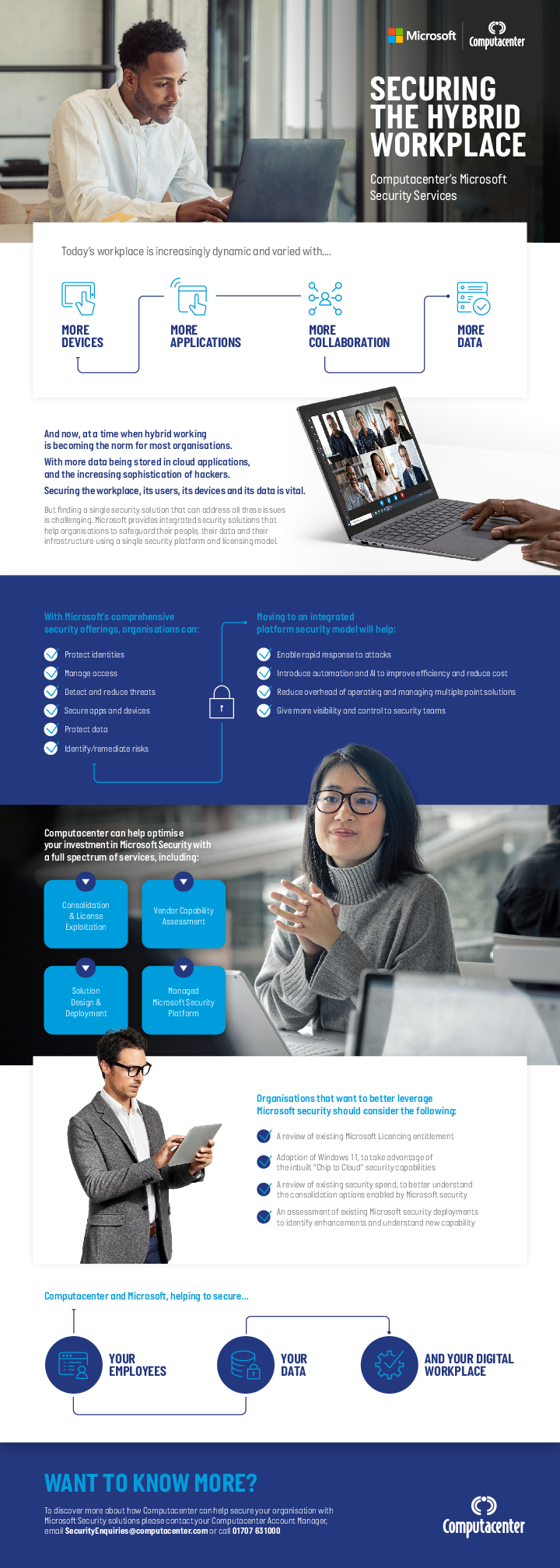
SECURING THE HYBRID WORKPLACE
Explore key insights on securing the hybrid workplace in our latest Infographic. This visual guide provides valuable information and practical tips to enhance your organisation's security in the evolving work landscape. Downloa...
MASTERING MICROSOFT SECURITY FOR THE MODERN WORKPLACE
Elevate your cyber security strategy with valuable insights from the latest eBook. Discover practical guidance and expert perspectives on navigating digital threats. Access essential information to fortify defenses and stay inf...
How good documentation fuels productivity
Learn best practices on how to organize and centralize knowledge so your team can work more efficiently and make decisions faster. In this webinar, you’ll get insights into: Building frameworks to centralize your team and compa...
Launch Wizard for SAP on AWS
In today’s episode, we will talk about what AWS Launch Wizard for SAP is all about, key features that the users should be aware about followed by merits and demerits of AWS Launch Wizard for SAP.
Accelerate SAP workloads recovery on AWS
Accelerate SAP workloads recovery on AWS. YASH’s expertise in cloud migration & modernization, building robust DR strategy and focus on customer success makes them a strong partner for clients looking to leverage AWS servic...
Driving Innovation Led Business Growth with SAP on AWS for a Middle-East Seafood Industry Leader
Driving innovation and tech-led business growth with SAP on AWS for a leading seafood enterprise. Driving Innovation Led Business Growth with SAP on AWS. See how AWS, SAP and Yash came together to support a leading seafood Ent...