Selecting Your Next-Generation Firewall Solution
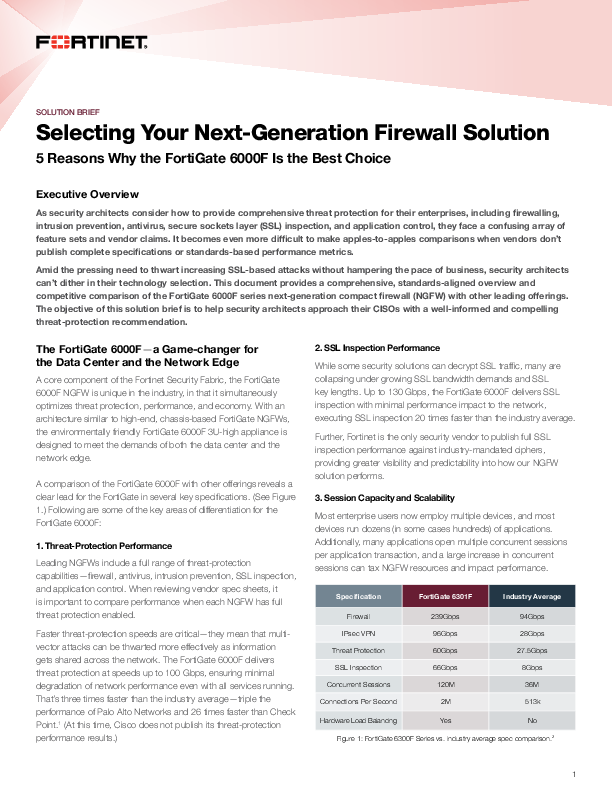
As security architects consider how to provide comprehensive threat protection for their enterprises, including firewalling, intrusion prevention, antivirus, secure sockets layer (SSL) inspection, and application control, they face a confusing array of feature sets and vendor claims. It becomes even more difficult to make apples-to-apples comparisons when vendors don’t publish complete specifications or standards-based performance metrics. Amid the pressing need to thwart increasing SSL-based attacks without hampering the pace of business, security architects can’t dither in their technology selection. This document provides a comprehensive, standards-aligned overview and competitive comparison of the FortiGate 6000F series next-generation compact firewall (NGFW) with other leading offerings. The objective of this solution brief is to help security architects approach their CISOs with a well-informed and compelling threat-protection recommendation.