A Checklist for Cloud Data Management
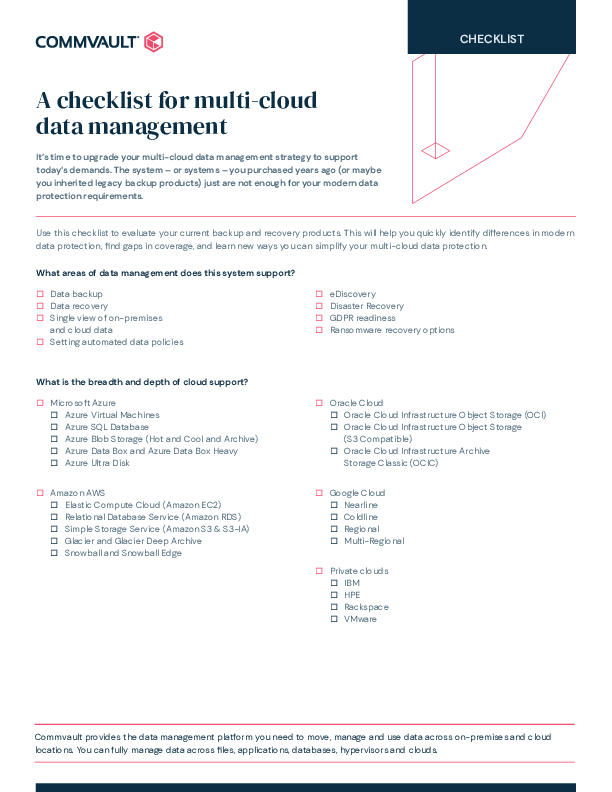
Upgrade your data management strategy to support today’s demands. The system – or systems – you purchased or inherited years ago are probably not appropriate for the modern data protection needs of your organization.
Use this handy checklist when you’re researching data protection that supports files, applications, databases and hypervisors, plus both public and private clouds.

Provider: Commvault Systems Ltd | Size: 282 KB | Language: English