白皮書存檔
Turning Policy Shifts into Moments of Clarity: Five Tips for Safeguarding Your Spend in Times of Change
Business change of any kind tells us two things. First, businesses inevitably gain an advantage, no matter if the adjustment is severe or minimal. Second, additional changes in how people get things done also emerge ‒ some shor...
Running the Numbers The key to your spend management story
The truth is always in the numbers, but it also often hides there – under a few mistakes figures in the mileage logbook, behind missing auditing, or in cash transactions that could or should have been put on a card. And the onl...
Achieve your best RTOs and RPOs
In an increasingly digital world, all organizations, across all industries, are susceptible to disruptions resulting in downtime and data loss. Given enough time, it is almost guaranteed that your organization will encounter a ...
Manage and Mitigate the High Cost of Ransomware
Get Ransomware Ready with Zerto Ransomware is one of the most dangerous threats to organizations around the world, and both the threat and the cost of ransomware attacks are continuing to grow. If you are not prepared for an a...
Modernizing Data Protection in a Hybrid World for Financial Services
PeerPaper™ Report 2022 Financial services firms need to balance strict security and compliance requirements with mandates for digital transformation and customer expectations for an “always on” business. Data protection, in pa...
Security Operations Maturity Model
As the threat landscape continues to evolve, your cybersecurity efforts must follow suit. With your security operations center (SOC) at the core of your offense against threats, you must ensure that it can handle anything that ...
Modernizing Your SOC Strategy
Modernizing your security operation center (SOC) strategy means investing your time, budget, or resources to enhance security maturity, improve resilience against cyberattacks, and reduce risk to the business in the modern-day ...
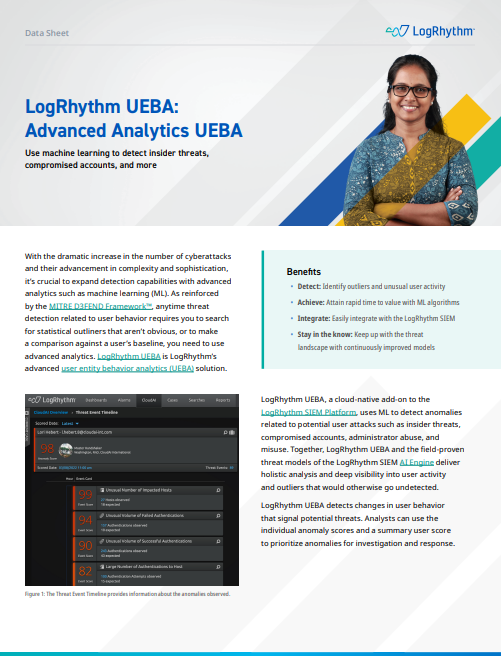
LogRhythm UEBA: Advanced Analytics UEBA
With the dramatic increase in the number of cyberattacks and their advancement in complexity and sophistication, it’s crucial to expand detection capabilities with advanced analytics such as machine learning (ML). As reinforced...
LogRhythm SIEM
For organizations that require an on-prem solution due to regulatory requirements or IT preference, LogRhythm SIEM is the industry’s most complete platform, providing the latest security functionality and analytics. LogRhythm S...
LogRhythm Axon
There is a lot riding on the shoulders of your security operations team — protecting the organization’s reputation; safeguarding sensitive client information and ensuring the organization’s ability to deliver products and servi...