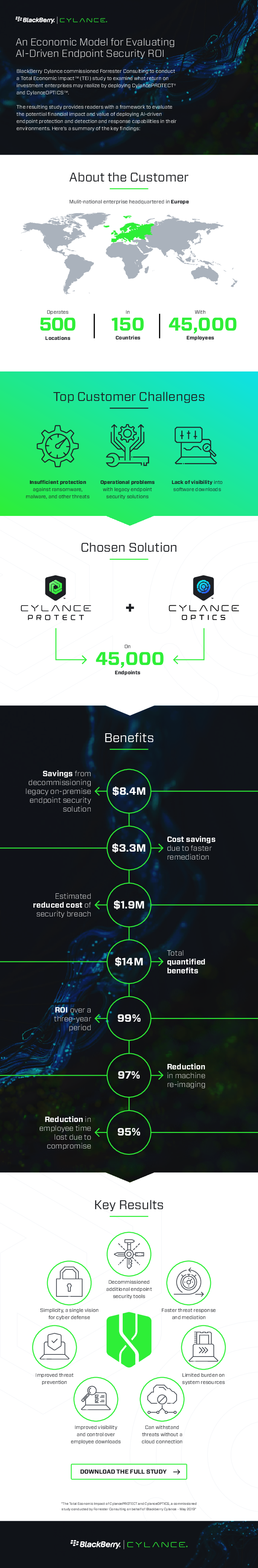
An Economic Model for Evaluating AI-Driven Endpoint Security ROI
BlackBerry Cylance commissioned Forrester Consulting to conduct
a Total Economic Impact™ (TEI) study to examine what return on
investment enterprises may realize by deploying CylancePROTECT®
and CylanceOPTICS™.
The resulting study provides readers with a framework to evaluate
the potential financial impact and value of deploying AI-driven
endpoint protection and detection and response capabilities in their
environments. Read this infographic to learn about the key findings.
Anbieter: Blackberry Cylance | Größe: 1,27 MB | Sprache: Englisch