白皮書存檔
Detecting Compromised Systems: Analysing the top eight indicators of threat traffic
Key indicators of a compromise can be found by analysing the network traffic from outbound connections—specifically, traffic coming from an endpoint on your internal network and connecting through your firewall to something on ...
Dissecting a Cloud Attack: Securing Azure with AzLog
Just because data, applications, and systems exist in Azure doesn’t mean your commitment to security, ability to monitor, and need to achieve compliance are any less. First, you need to collect security events, configuration ch...
User and Entity Behaviour Analytics: Protecting your organisation from within
Organisations are built around technology, but that technology is still controlled and managed by human hands. For a network to remain secure, both internally and externally, trust is an essential ingredient. Employees need acc...
CISOs Investigate: User Behavior Analytics
CISOs Investigate: User Behavior Analytics (UBA) includes interviews with 11 security leaders who have deployed or are looking to deploy third-party solutions. This report replaces the ad hoc, often informal and time-consuming ...
Managing User Risk: A Review of LogRhythm CloudAI for User and Entity Behavior Analytics
In this review, we explored the recently released LogRhythm CloudAI, which provides user-focused behavioral analysis built into LogRhythm. CloudAI encompasses a robust NextGen SIEM solution to extend recognition of user threats...
Market Guide for User and Entity Behavior Analytics
Security and risk management leaders considering UEBA will find that the market has fragmented, with a few pure-play vendors and a wide set of traditional security products that embed core UEBA technologies and features to bene...
Networking and Information Systems (NIS) Directive
The EU’s Network and Information Systems (NIS) Directive entered into force in August 2016 with the aim of increasing the resilience of cybersecurity defences across Europe. The clock is now ticking with EU member states having...
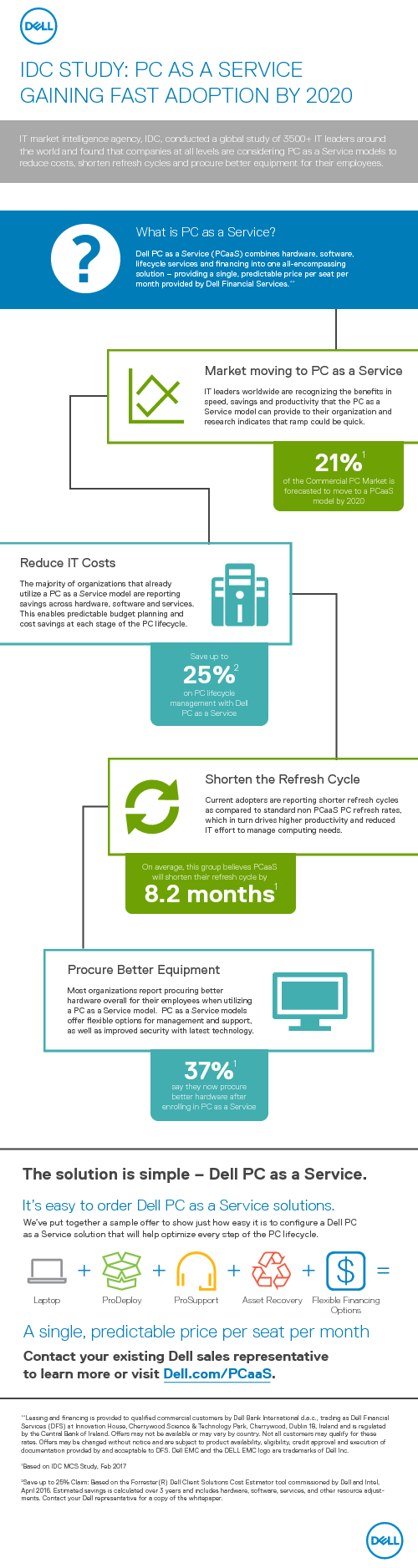
IDC STUDY: PC AS A SERVICE GAINING FAST ADOPTION BY 2020
Traditional PC lifecycle management is an inefficient and expensive process that will cost your business both time and money. Dell EMC’s PC as a Service (PCaaS) will transform your company’s approach to IT infrastructure. IT m...
The Rise of the Micro PC - Security and End User Productivity Benefits
As employee mobility increases globally and enterprise investments shift to tablets and laptops, organizations are assessing their ongoing investment in traditional PCs. One thing that remains clear is that enterprise PC buyers...
Optimizing Your Endpoint Security Practice For Effective Ransomware Protection
Advanced endpoint threats and steady attacks change the way that decision-makers at organizations of all sizes and across industries prioritize, purchase, and execute on security initiatives. Now more than ever, IT security pro...