Whitepaper-Archiv
Lessons Learned aus echten Cyberangriffen
7 Tipps, mit denen Sie Ihr Unternehmen besser schützen Nie war die Gefahr von Cyberangriffen größer, als es aktuell der Fall ist. Jetzt gilt es, sich optimal vorzubereiten. Dabei können die Erfahrungen helfen, die andere bere...
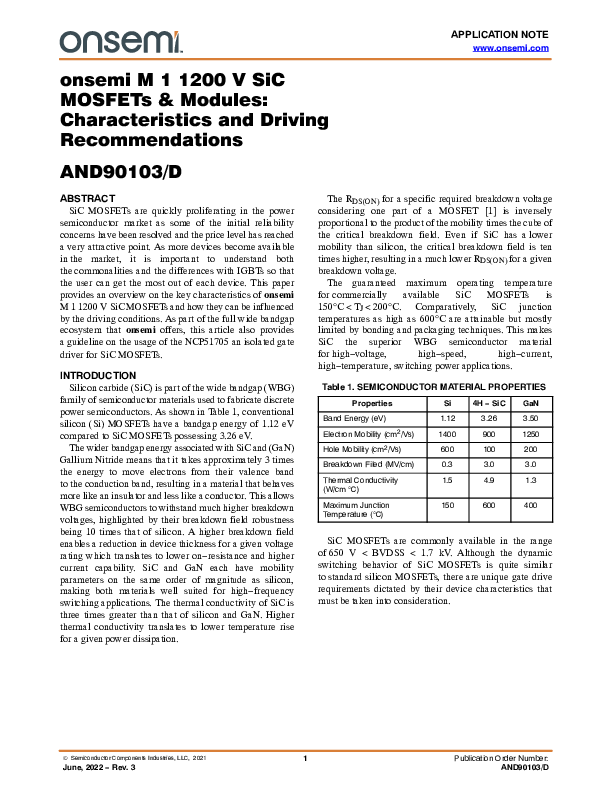
onsemi M 1 1200 V SiC MOSFETs & Modules: Characteristics and Driving Recommendations
SiC MOSFETs are quickly proliferating in the power semiconductor market as some of the initial reliability concerns have been resolved and the price level has reached a very attractive point. As more devices become available in...
Performance Comparison of 1200 V SiC MOSFET and Si IGBT Used in Power Integrated Module for 1100 V Solar Boost Stage
This application note compares the performance of two power integrated modules (PIMs) in the boost stage of an 1100 V solar inverter. One PIM used state−of−the−art silicon 1200 V IGBT (part number NXH100B120H3Q0 defined as PIM−...
Fast DC EV Charging: Common Topologies and Power Devices Used in the System
The role of DC Fast charging (DCFC) is clear in removing barriers to EV adoption. The need for shorter charging times has resulted in higher power EV fast charging approaches 400 kW entering the market. In this paper, we will d...
SiC MOSFETs: Gate Drive Optimization
For high−voltage switching power applications, silicon carbide or SiC MOSFETs bring notable advantages compared to traditional silicon MOSFETs and IGBTs. Switching high−voltage power rails in excess of 1,000 V, operating at hun...
2022 Threat Report
Der BlackBerry 2022 Threat Report ist mehr als nur ein Rückblick auf spektakuläre Cyberattacken von 2021. Er bietet Ihnen einen dezidierten Überblick über die weltweiten Herausforderungen, die sich direkt oder indirekt auf die ...
Cloud Security Services
The security landscape has changed drastically in recent years. Today, companies work across distributed cloud environments, while end-users need anytime, anywhere access to data. Instead of securing the perimeter to keep thre...
6 myths of SIEM - Early visibility and rapid response to threats in your environment
To say that security is a hot topic right now is an understatement. The threat landscape has changed drastically in recent years, meaning that every company needs to rethink or review its approach. In the new world of security...