Архив проектных документов
Поиск
доступные документы: 11724
Новейшие темы:
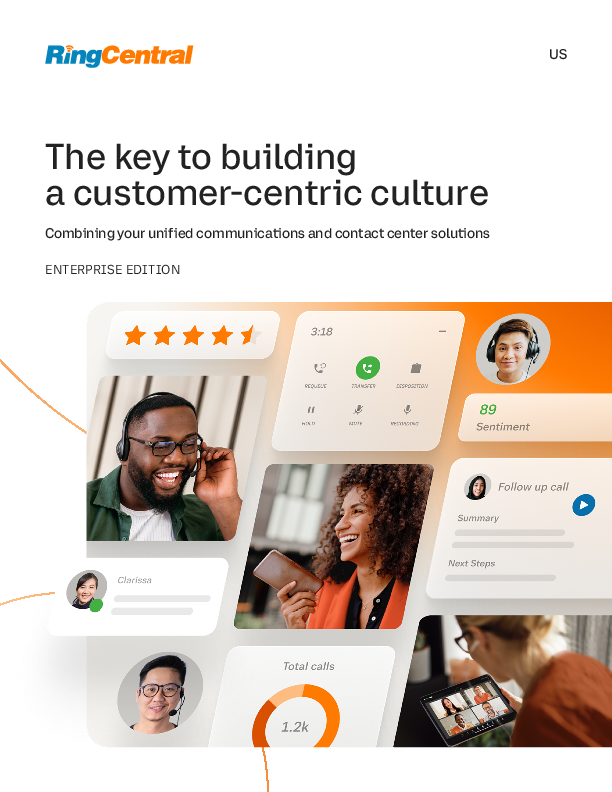
The key to building a customer-centric culture: Combining your unified communications and contact center solutions
Смотреть электронную книгу
Virtual Event: Maximizing Cost Efficiency of Migrating to Public Cloud, taking place on Thursday, 15 May, 2025 3.30PM BST | 4.30PM CEST | 6.30PM GST
Смотреть вебинар для просмотра по запросу
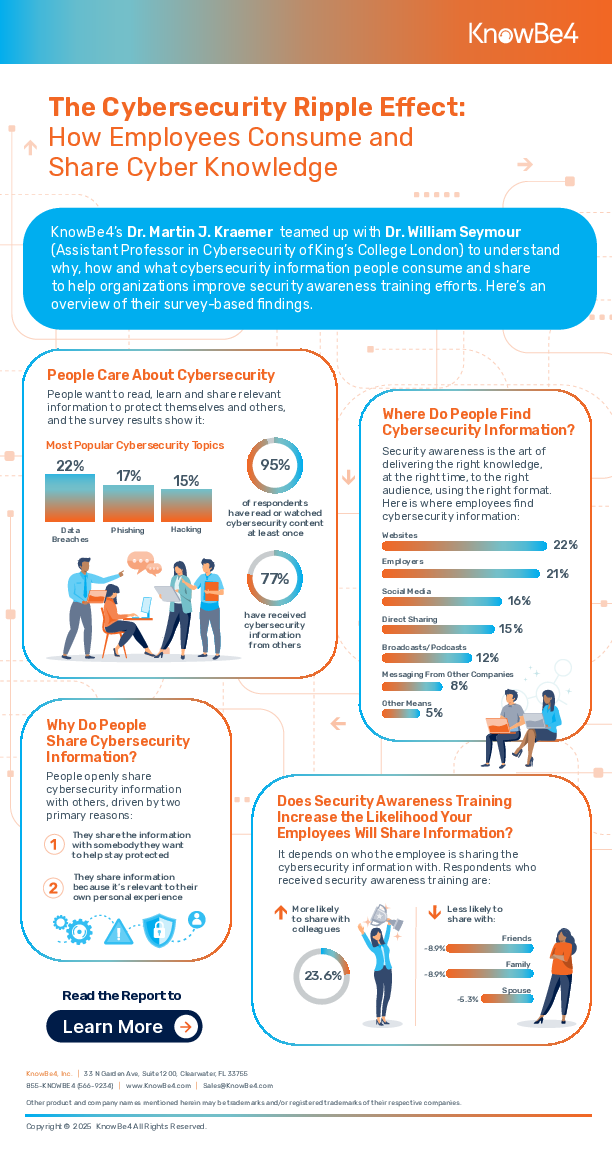
The Cybersecurity Ripple Effect: How Employees Consume and Share Cyber Knowledge
Смотреть инфографику
Регистрируйтесь для получения нашей рассылки
Самые важные новости бесплатно по электронной почте