Arquivo de Documentos Técnicos
Modern Adversaries & Evasion Techniques
If you take away one thing from this eBook, make it this: Legacy antivirus (AV) is no longer capable of stopping adversaries. Modern endpoint security is required to stop breaches — period. Where did legacy AV go wrong? First, ...
KuppingerCole Leadership Compass 2023: Access Management
In Today's Threat Landscape, Identity Security Requires a Leader Learn how CyberArk achieved a distinguished leadership position in the 2023 KuppingerCole Leadership Compass for Access Management report and secured top honors ...
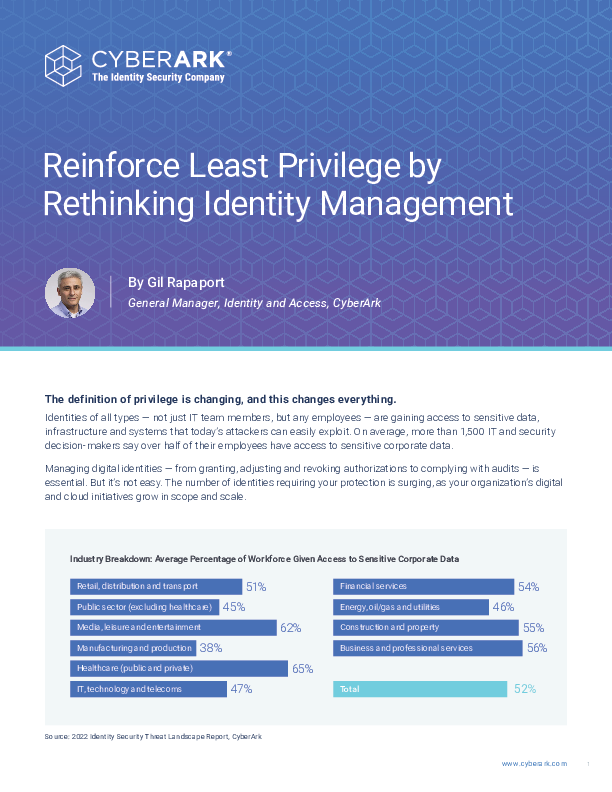
Reinforce Least Privilege by Rethinking Identity Management
Why It's Time to Rethink Your Identity Management Approach Identities of all types - not just IT team members, but any employees - are gaining access to sensitive data, infrastructure and systems that today’s attackers can eas...
Identity and Access Management is Leading the Way for Identity Security
Future-Proof Your Organization's Identities In recent years, Identity and Access Management has rapidly evolved. Learn how your organization can keep up with these changes by exploring automation, overcoming identity security ...
Secure Identities with the Power of Modern MFA
Secure Identities with the Power of Modern MFA Multi-factor authentication (MFA), when set up correctly, can help enterprises better protect identities, mitigate risks and secure access for the entire workforce. This eBook fea...
Secure Access for the Identities Driving Your Key Initiatives
What’s the connection between transformation and threat? While external actors are responsible for 83% of breaches,let’s look beyond the perpetrators and focus on the identities under attack. Often the risks link to the second-...
Critical Gaps in Securing Identities
Benchmark Your Identity Security Strategy Enterprises today rely on hundreds of applications to achieve their business and operational goals, yet there are significant challenges in securing applications that sit outside of t...
Generative AI and LLM School
Get started on your LLM app development journey with an introduction to key technical concepts so that you can then jump into demos and see how easy it is to build chatbots and other apps, all inside Snowflake. Hear from indust...
Generative AI and LLMs For Dummies®, Snowflake Special Edition
Generative AI (gen AI) and large language models (LLMs) are revolutionizing our personal and professional lives. From supercharged digital assistants that manage our email to seemingly omniscient chatbots that can communicate w...
INTRODUCTION TO SNOWFLAKE
Get a short, 20-minute introduction to Snowflake. Learn how businesses including Deliveroo, Allianz, and Penguin Random House scaled their businesses, reduced costs, and increased productivity by using Snowflake. A product expe...