Archivio whitepaper
RSA NetWitness Orchestrator
In an era of ever-expanding attack surfaces, protecting against threat actors—from commodity malware, insider threats and crimeware to state-sponsored exploits, hacktivists and terrorists—has become an increasingly complex acti...
The Ransomware Threat: A guide to detecting an attack before it’s too late
Is your organisation prepared for a ransomware attack? Successfully defending your organisation against such an attack takes preparation and an understanding of what to look for if an attack begins. This guide shares the expe...
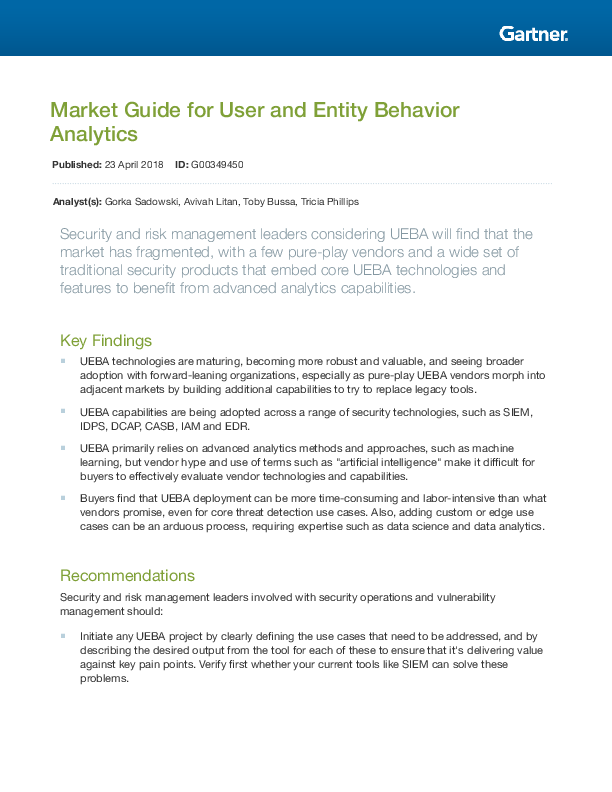
Gartner Guide: Market Guide for User and Entity Behavior Analytics
Security and risk management leaders considering UEBA (User and Entity Behavior Analytics) will find that the market has fragmented, with a few pure-play vendors and a wide set of traditional security products that embed core U...
CISOs Investigate: User Behaviour Analytics
UBA will likely be one of the more valuable additions to the technology stack. Security leaders can learn a lot and potentially apply technologies and processes from other functional areas. UBA is a derivative of other useful b...
Employing Machine Learning in a Security Environment: A data science-driven approach
No matter where you look in the security world today, you’ll see the terms machine learning and artificial intelligence (AI). There’s been a great deal of interest in machine learning and AI as security vendors and their custom...
Build a strategic approach to network and app security
How to secure your entire digital ecosystem. Users want choice when it comes to their apps and devices, and the flexibility to work anywhere, anytime. But that creates a lot of undo complexity, security risk, and systems sprawl...
Unlock opportunity with a new security approach
Gain the flexibility and control you need to advance innovation, manage risk, and enable new ways of working.
Deliver secure, contextual user access on any device anywhere, without sacrificing IT control
Citrix offers a comprehensive security approach that delivers the secure contextual access you need to provide an enhanced user experience while you maintain control.
Reducing cyber risk in the legal sector – The blurred boundaries of trust
How legal firms can adopt best practice through the adoption of security intelligence tools. This paper examines the top five use-cases for centralised monitoring within the legal sector, in order to reduce cyber risk through ...
The Threat Lifecycle Management Framework
Prevent major data breaches by reducing time to detect and respond to threats Globally, sophisticated cyber-attacks are compromising organisations at an unprecedented rate and with devastating consequences. Modern attackers, i...