سجل المستندات التعريفية
4 Essentials For Turning The IoT Into Actionable Intelligence
Edge computing will soon become the new norm as we enter the era of zettabytes and billions of connected devices. Dell EMC PowerEdge servers are uniquely designed to meet the demands of edge computing with integrated security, ...
SAP Business Transformation Study: Wie fördert man unternehmensweit den Teamgeist?
Ob geschäftlich oder privat, Millionen Menschen nutzen täglich die Dienste von Telefónica Deutschland. Telefónica Deutschland ist nicht nur der größte Mobilfunkbetreiber des Landes, sondern bietet auch Festnetz- und Breitb...
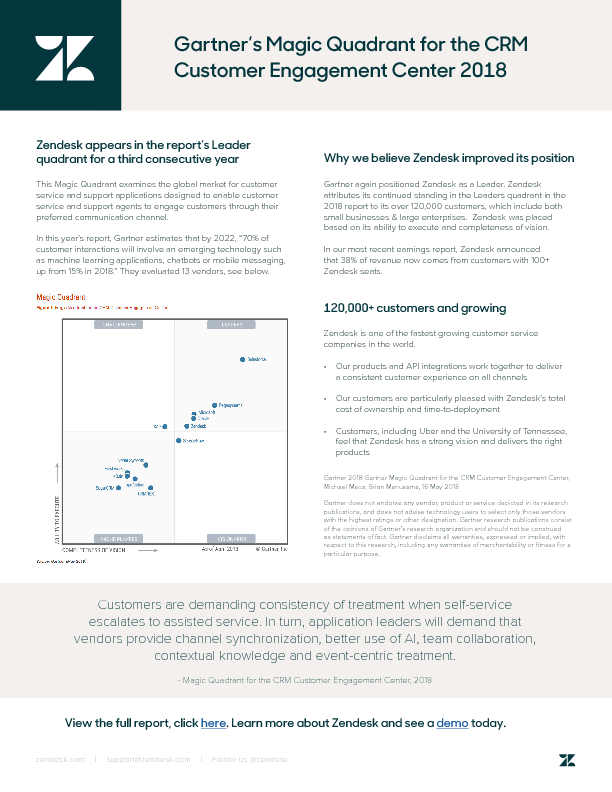
Gartner’s Magic Quadrant for the CRM Customer Engagement Center 2018
In the global market for customer service software, Zendesk is once again recognized as a leader in the 2018 Gartner Magic Quadrant for the CRM Customer Engagement Center. Every year, Gartner conducts a thorough analysis of se...
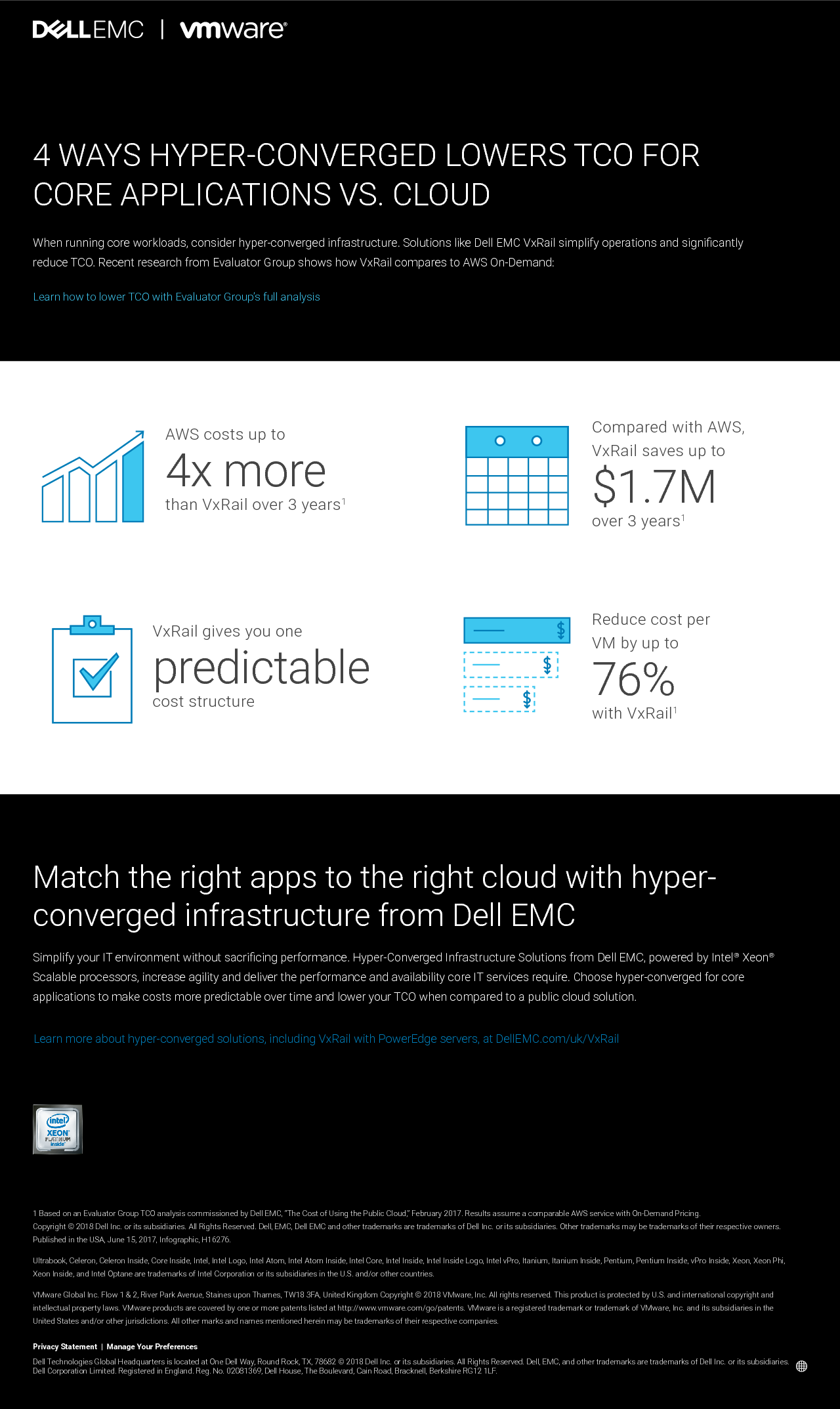
4 ways Hyper-Converged lowers TCO for Core Applications vs. Cloud
Simplify your IT environment without sacrificing performance. Hyper-Converged Infrastructure Solutions from Dell EMC increase agility and deliver the performance and availability core IT services require. Choose hyper-converged...
Gain Internet of Things insight from Machine Learning with SAP and Red Hat
Across industries, Internet of Things (IoT) devices collect massive volumes of detailed data about their characteristics and operating conditions. The data from each device can be compared with a large dataset collected from si...
Overcoming Alert Fatigue in a Modern Ops Environment
Alerts from monitoring systems and ticketing tools are a good thing, as they help IT Ops and DevOps teams track the health and performance of core apps and services, and enable responders to react quickly to incidents. But it’s...
The State of IT Work-Life Balance
A new survey on the State of IT Work-Life Balance reveals that poor work-life balance affects an IT professional’s ability to manage stress, leading to high turnover as professionals seek a better work environment. The survey a...
Measuring the ROI of DevOps
DevOps is a culture, movement, or practice that emphasizes the collaboration and communication between software developers and IT operations professionals, while automating and accelerating the process of software delivery and ...
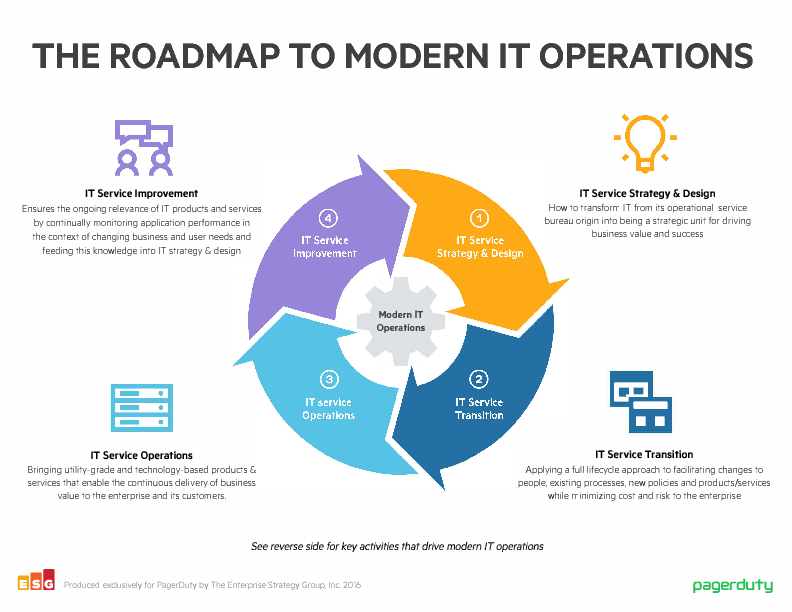
The Roadmap To Modern IT Operations
This infographic shows the key activities that drive modern IT operations: - IT Service Strategy & Design - IT Service Transition - IT Service Operations - IT Service Improvement
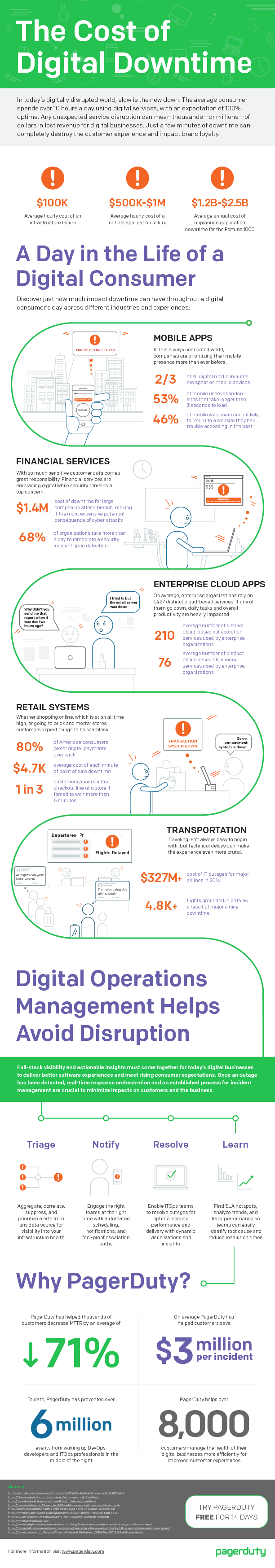
The Cost of Digital Downtime
In today’s digitally disrupted world, slow is the new down. The average consumer spends over 10 hours a day using digital services, with an expectation of 100% uptime. Any unexpected service disruption can mean thousands—or mil...